FlexiHub Team uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our cookie policy. Click here to learn more.
USB over Ethernet (also called USB over Network or USB over IP) solution allows you to share USB-based devices over Ethernet, Wi-Fi, LAN, or even the internet. With its help, you can operate printers, webcams, scanners, and other USB devices over a distance and can access data from a USB flash drive connected to a remote machine.

The most convenient way to access USB over Ethernet is by using special software or hardware, like an adapter, a hub, and a USB to Ethernet cable.
In this article, we want to help you to choose the best USB sharing software for your needs.
It’s critically important to choose the right tools when it comes to hardware-based sharing of a USB through Ethernet. Depending on your specific situation, you may need an adapter, a USB hub, a CAT5e cable extender, or some other wires and gadgets.
Share USB via Ethernet with a dedicated software solution (e.g., FlexiHub) works for all types of USB peripherals and operating systems, and that alone makes this method so popular. Plus, a software USB extender has no limits on distance or the number of USB ports you can share. And you won’t have to spend money on any extra gadgets (like a USB hub or USB-RS32 adapter) and CAT6 LAN cabling.
So before you start spending on any of these, please, make sure you’ve reviewed USB over Ethernet systems comparison. The variety of hardware and software tools for USB redirection can be confusing, so here is the comparison chart of the top solutions on the market:
|
|
|
| ||||||
|---|---|---|---|---|---|---|---|---|
| License type | Various subscription plans | N/A | N/A | |||||
| Subscription options |
• Personal: 3 connections*/5 nodes**
• Team: min. 5 members
• Business: custom
|
N/A | N/A | |||||
| Free demo limitations |
5 shared devices
30 days |
N/A | N/A | |||||
| Price per device | USD 13.25 | USD 14.99 | USD 13.49 | |||||
| Multiple device log-in | up to 5 nodes/account*** | N/A | N/A | |||||
| Proxi-server |
Redirection Server
• no need for external IP • multi-network communication • works through the Firewall |
N/A | N/A | |||||
| ||||||||
| Firmware for microcontrollers | Raspberry (upon request) | N/A | N/A | |||||
| Security |
Login tokens for safe account sharing
Lock for device access control
|
N/A | N/A | |||||
| Encryption | 2048-bit SSL | N/A | N/A | |||||
| RDP support | N/A | N/A | N/A | |||||
| COM-port devices support | Windows only | N/A | N/A |
* Connection number defines how many remote devices you can connect to over the network at the same time
** Node is a machine you can log into your account on
*** You can have more for an extra fee
Modern USB over Ethernet apps are as reliable as any physical gadget, cost much less, and often have some handy extra features to offer. Let's overview the complete 2022 Top-6 list.
Price: From $14/month
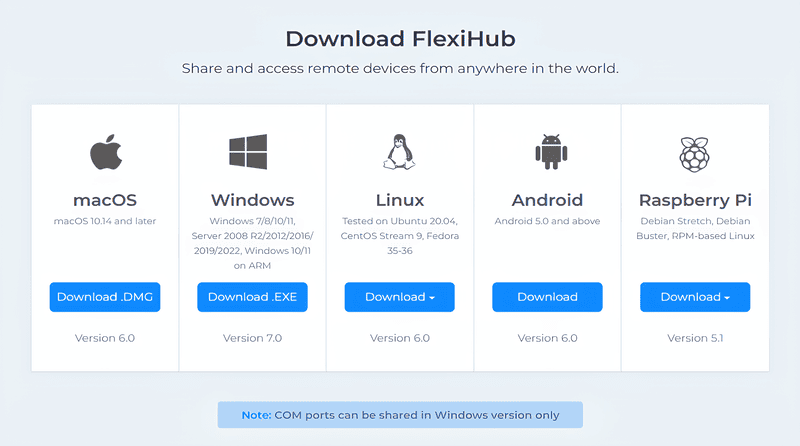
Supported OS: Windows, Linux, macOS, and Android
Demo Limitations: 30 days / you can establish up to 5 sessions
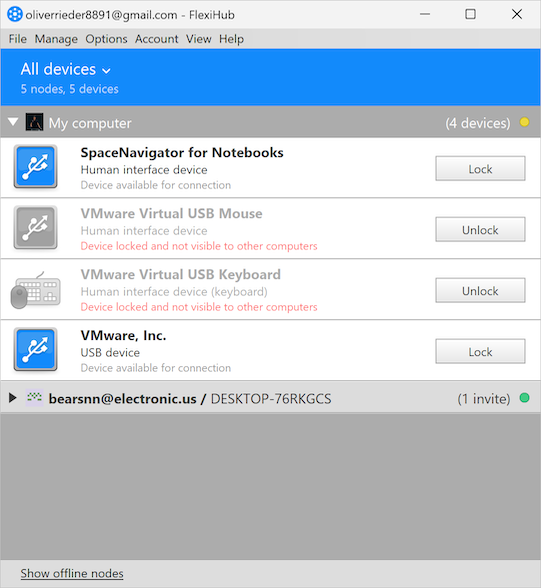
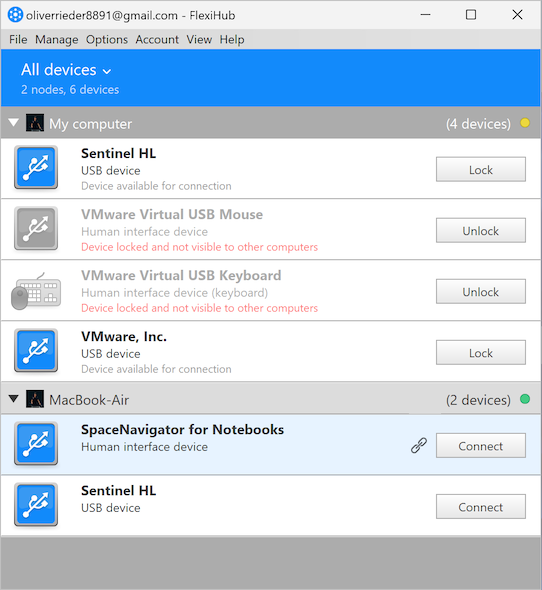
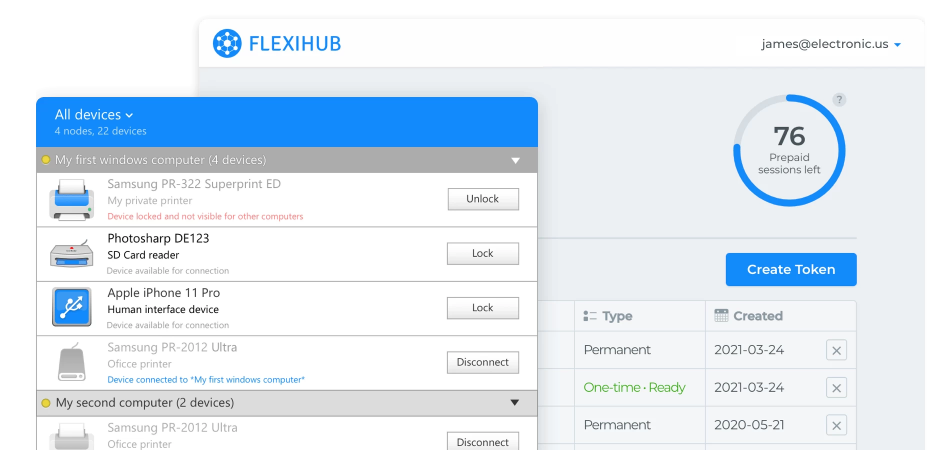
FlexiHub holds the leading position in the field of USB over Network solutions. The main winning points of FlexiHub owe its popularity to are:
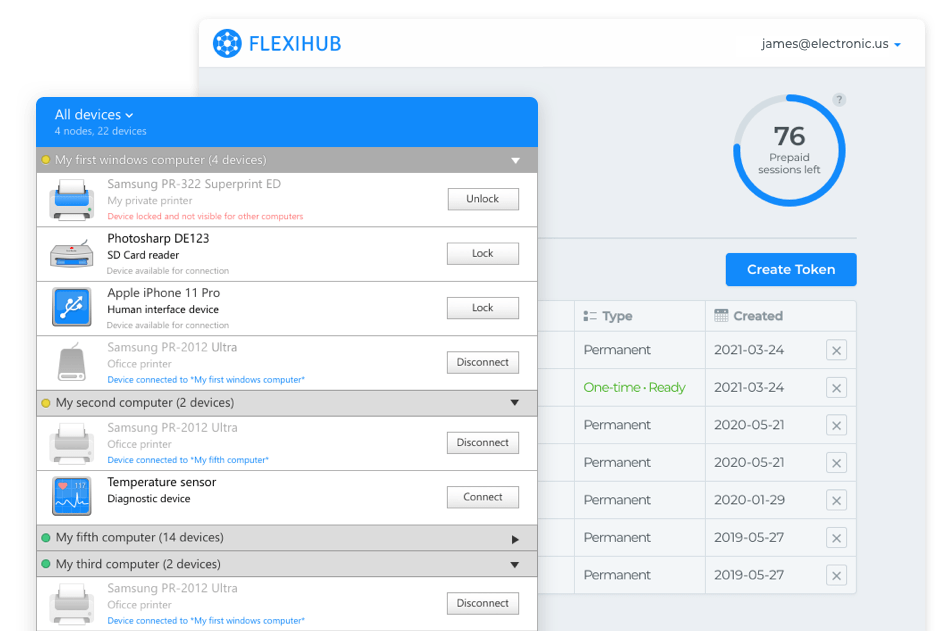
Let’s find out what makes FlexiHub so unique and exceptional!
There are many more technical benefits of FlexiHub we can name, but let’s get to the reasons why this solution can be a perfect fit for your needs.
Some work remotely with the team that needs to access devices in the office or on a thin client. Or, in a particular case, you may want to access your favorite hardware (dongle, printer, etc.) you don’t want to replug all the time. Are you a business owner looking for a way to cut your expenses and switch to remote operation?
None of the other solutions listed below have such flexible terms and conditions of use as FlexiHub.
For individual users, FlexiHub is the easiest solution possible. One-click, and you have access to any USB or COM device no matter the distance!
For businesses, it has high-capacity service plans with custom software branding and precise customization for your specific business needs. Our sales team will work with you to ensure the developers' crew fulfills your every requirement to the fullest extent.
For a team that needs access to the same devices, FlexiHub offers a team account with centralized monthly billing and convenient user management that allows secure collaboration within and outside the team.
Price: Starts from $159.95
Supported OS: Windows, Linux, macOS, Android
Trial limitations: 14-day trial, You can share only one local USB-device
USB Network Gate by Electronic Team, Inc. should be on your radar if you need a software tool that works better than any hardware USB-Ethernet adapter. It is an effective USB extension app that turns a machine into a USB server that reliably redirects traffic from USB-based devices across a network.
USB Network Gate provides a convenient way to share printers, dongle keys, card readers, web cameras, and any other peripheral plugged into a USB port of your computer over any network, including WiFi, Ethernet, LAN, or the Internet.
USB Network Gate helps resolve the issues of accessing local a USB device from VMware, VMware ESX, Citrix XenDesktop, and Microsoft Hyper-V virtualization environments.
The solution lets you share USB over the Remote Desktop Protocol, making it simple to work with a local USB device in a remote session.
In a shared computer environment, use USB Network Gate to isolate any connected USB devices and prevent unauthorized access. With any USB peripheral device, whether it’s a USB drive, camera, or audio card, you can manage access by specifying a session ID or a specific user by a Microsoft user account
USB Network Gate can compress traffic. This allows for improving the data transfer speed and optimizes bandwidth usage, so the high-speed 100 Mbps connection is not required. The app supports advanced 256-bit SSL encryption that guarantees the security of your communications. It's especially important when you share USB cameras or license dongle keys all over your network.
Price: $49
Supported OS: Server runs on the Synology, QNAP, ASUSTOR, ReadyNAS, and MyCloud NAS Devices, Raspberry Pi, AMD64, x86, MIPS, ARM, PowerPC, ARM64, etc. running ANY version of Linux, and now runs on OSX, Android and Windows AND WSL2
Trial limitations: 14-day trial, You can share only one local USB-device
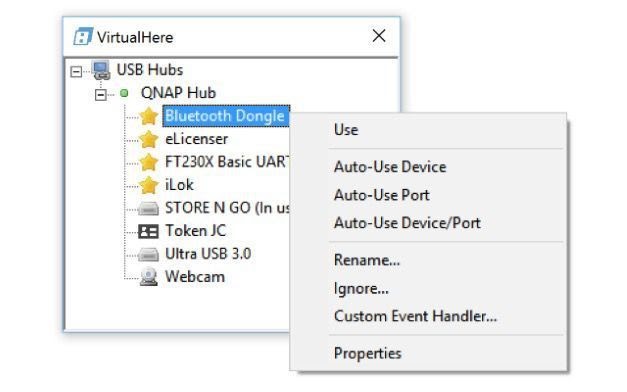
VirtualHere is a handy app that eliminates the need to physically plug USB devices into your computer when you want to use them. With this solution, your valuable peripherals can be accessed remotely over a local network, the Internet, or in the cloud.
The app has a clean and friendly GUI and requires minimal effort to be installed. It’s compatible with Windows, macOS, Linux, and Android. You can remotely access USB devices that are plugged into your NAS, which is also a great advantage.
Some other benefits you get with this app include a built-in VPN subscription service and a special version for network-attached storage.
Price: Starts from $149.95
Monthly-based licensing starts from just $10.70/month
Supported OS: Windows, Linux
Trial limitations: 15-day trial, only one USB device can be connected by the client.
Another great tool for remote access to USB-based devices is USB over Network by FabulaTech. The utility works perfectly well on Windows and Linux operating systems.
It gives you a way to connect to USB dongle keys and other peripherals even if they are located miles away from you. With this application, you get an effective USB server auto-discovery feature which allows you to find all USB servers installed in your local network without specifying their remote IP address.
Price: Starts from $54.99
Supported OS: Windows only
Trial limitations: no
USB over Ethernet by KernelPro is a software solution with two separate parts. A server-side app is used to share USB devices over the Internet (i.a., Wi-Fi), VPN, and local network connections. It has a very limited free trial version that lacks almost all advanced features and only allows one connection at a time, so it doesn’t really give you a complete impression.
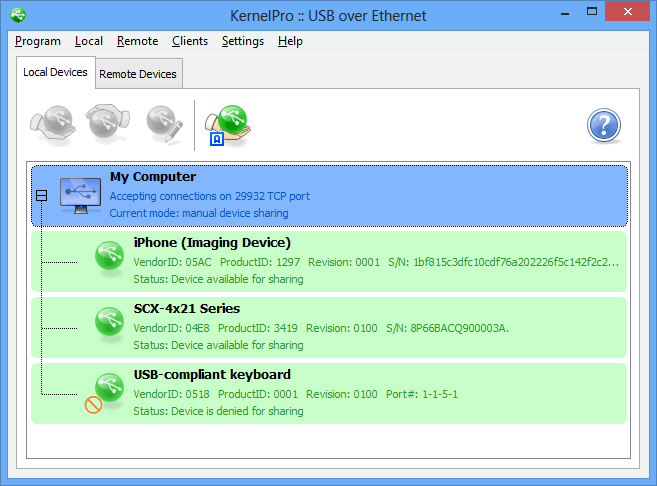
The client-side of this software is entirely free. It allows you to connect to the devices shared with the server-side app and use them just like you would use local devices directly connected to your machine.
The best features of USB over Ethernet are: USB device sharing/accessing, free client app, auto-reconnection, compatibility with Hyper-V, VMware, and other virtual machines
Note: This solution has no support for Windows 11
Here are some of the most common criteria users take into account when selecting a software USB extender:
Different software tools offer different levels of protection when redirecting USB data over the network. If you are going to share a peripheral over Ethernet, you should make sure your USB sharing application forwards your sensitive data over encrypted channels.
It’s important whether the solution can be utilized only as a standalone USB over Ethernet app or can be integrated into a custom product. Only FlexiHub has UI modification and White labeling options.
There are free and paid USB over network apps.
If you are developing your own product and your goal is to add some basic USB sharing capabilities to your project, the free solution may be sufficient. However, if you are looking for some advanced USB redirection features like remote access to USB devices over RDP, forwarding of USB to a virtual environment or a blade server, etc., it would be wise to consider a paid application with a powerful feature set.
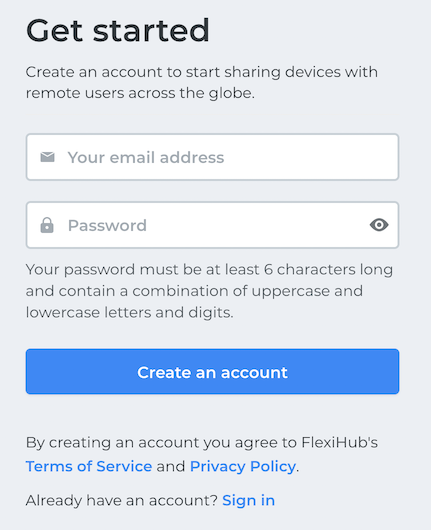
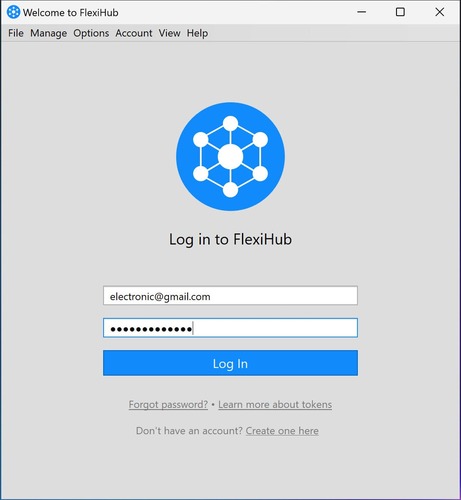
We’ve reviewed every critical aspect you need to consider while choosing a USB over Ethernet sharing solution. Don’t waste your time and try the demo version of FlexiHub right now! FlexiHub is the most easy-to-use tool. Once you sign in for your account, you can access any remote USB/COM port device in just a couple of clicks.